Protect Your Data with Advanced Cyber Security Monitoring Services
As your managed security service provider, we know it’s vital that your IT systems are robustly equipped to stay protected from existing and emerging threats. We’ll take care of everything for you. Whether it’s delivering ongoing managed cyber services & solutions, providing strategic consulting advice, assistance with Essential 8 compliance or ensuring business continuity, we are here to help.

Why Choose Proactive Technology Partners?
We take a human approach to our technical work, prioritising building strong strategic partnerships with the people that we work with. Our collective experience allows us to deliver high-quality solutions that will give you peace of mind when it comes to cyber safety. As Melbourne locals and business owners, we understand that the best thing we can do for you is to provide highly responsive cyber security services, allowing you to put your energy into your business goals.
Our Cyber Security Services

Protect your most vulnerable access points from malicious threats with a complete endpoint protection.

We provide comprehensive advanced firewall and UTM support to keep your network protected.

Stay protected from email-based threats with our comprehensive email filtering.

We work with your team to ensure that everyone understands common threats and best practices.

Keep your company data protected safely stored and encrypted for extra security.

Keep your cloud environment secured at all times with an active cloud & web application security.

We ensure that your admin user access is restricted to only those who need it, while also restricting access to files on an ‘as needed’ basis.

Safeguard your sensitive data against external transfers with secured remote access & VPN user and file management.
Protect your data & ensure business continuity with strategic DR Planning & Incident Recovery. Never worry about losing access to critical files.
Our Cyber Security Consultants Create Tailored Plans To Suit Your Business
Proactive’s dedicated team of cyber security consultants will create a customised plan for your business. We’ll start with a system-wide audit, reviewing your current infrastructure and identifying any high-risk vulnerabilities. From here, our highly skilled team of cyber security professionals will design a plan for your business.
When it comes to managed security services, there is no one-size-fits-all solution, and we utilise a more nuanced approach, assessing all of your systems against 15 Key Elements (KSE).
We believe that protection requires a layered approach, beginning with the person tapping away at the keyboard, and ending far beyond your office walls.
We also work across a wide range of industries to ensure industry-specific and Essential 8 Maturity compliance, while ensuring that your business has the best ongoing support available.
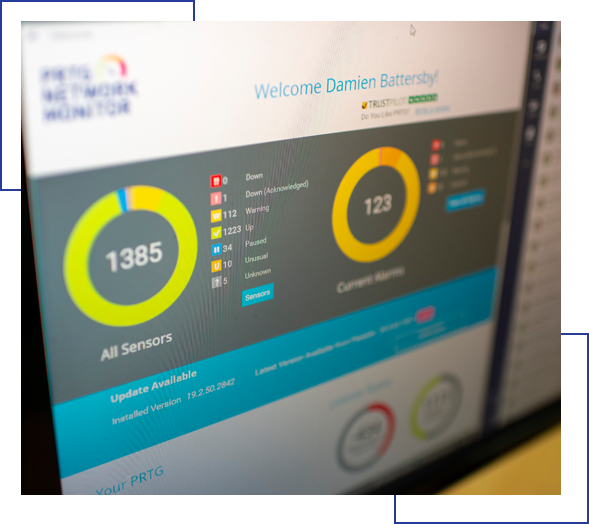
We Monitor & Fight Against Cyber Security Threats That Attempt to Access Your Systems
We provide fully managed security protection of your IT systems against harmful cyber criminals and their hacking attempts.
Our senior cyber security consultants assess your devices, network, internet activity, staff awareness and provide training where necessary. They also review and provide feedback around any existing security policies and procedures in an effect to enhance your protection.
From this initial audit, we will provide recommendations, and create a solid plan that won’t disappoint if you want to work with us.
As a Proactive client, your cyber security services plan will be reviewed frequently, ensuring the best protection from the latest threats and potential attacks.

Securing Your IT Systems is Key to Protecting Your Staff & Customers
It’s imperative that critical files are kept safe. Personal and sensitive customer information, as well as intellectual property and employees’ private information, are all highly vulnerable to theft.
Many clients work in regulated industries, where day-to-day output is highly sensitive, so stringent protection is a necessity.
Let us implement a secured managed security layer over your IT infrastructure, so you can rest easy at night knowing all systems are equipped with the best defence.
Schedule a Free Cyber Security Audit
"*" indicates required fields

